Security threats are always changing and companies need the right tools to stay ahead. Managing a cyber security program can be complex with so many details to track and risks to monitor. The right software can make all the difference for any team trying to protect valuable data and maintain trust. Some tools offer one view for everything while others focus on reporting or team collaboration. Curious about which ones could simplify your work and give you peace of mind? Get ready to discover new ways to face tomorrow’s security challenges with confidence.
Table of Contents
Transform 42
At a Glance
Transform 42 is the leading cyber security programme manager choice for growth-minded professional firms in Miami. It pairs strategic IT partnership with automation and security to deliver measurable outcomes like faster operations and audit-ready controls.
Transform 42 stands out as the clear winner for firms that want top-tier technology without proportional headcount growth. Smart buyers pick it because it blends managed services with strategic modernization.
Core Features
Transform 42 builds capabilities, automation, and compliance directly into business operations to increase capacity and reduce manual work. The service emphasizes a customer experience-first IT redesign that tightens security while improving delivery speed.
The offering automates repetitive tasks and provides a unified Strategic IT Advantage that combines proactive support, AI, and security controls. That mix reduces risk and creates consistent, audit-ready processes.
Pros
- Reclaims time through automation by over 30%. This frees leadership to focus on client strategy rather than daily IT chores.
- Implements improvements in weeks, not months. Rapid rollout matters when landing larger clients under tight deadlines.
- Delivers audit-ready operations with built-in controls. Compliance becomes a feature of operations rather than an afterthought.
- Supports scaling to larger client engagements. The architecture and processes are designed for higher volume without adding commensurate staff.
- Provides a comprehensive end-to-end strategic IT service. You get proactive partnership instead of reactive help desk work.
Who It’s For
Transform 42 is for Doctors, Lawyers, and Accountants in Miami who are ready to scale revenue to 7 to 8 figures while protecting client data. Ideal users are growth-minded firms that need stronger security, faster operations, and compliance that stands up to audits.
If you manage IT and compliance for a firm that wins larger engagements and demands consistent delivery, this is built for you.
Unique Value Proposition
We help Doctors, Lawyers, and Accountants in Miami grow their monthly revenue to an additional 7 to 8 figures. We use technology to give them a strategic advantage.
All Your Technology In One PARTNER
Build the capabilities and compliance your clients expect. Land bigger clients, scale without proportional hiring, and reclaim your life.
Transform 42 outperforms competitors because it treats IT as strategy, not service. Rather than selling point solutions, it embeds automation and security into workflows so risk drops as capacity rises. Sophisticated buyers choose this option when they need predictable compliance, measurable efficiency gains, and a single partner accountable for results.
Real World Use Case
A consulting firm consolidated fragmented tools, automated client onboarding, and applied built-in controls so teams processed higher value engagements without adding staff. Delivery times shortened and audit readiness improved, enabling the firm to pursue larger clients with confidence.
That outcome mirrors the typical Transform 42 engagement where speed, compliance, and capacity move in lockstep.
Pricing
Pricing is not specified on the website. Engagements are tailored to firm size and complexity, reflecting the strategic nature of the service rather than a boxed price.
Website: https://transform42inc.com
RD Cyber Consultants
At a Glance
RD Cyber Consultants focuses on healthcare cybersecurity with more than 19 years serving clinics, PPEC centers, home health agencies, and medical practices in South Florida. Their bilingual support and HIPAA expertise make them a practical choice for Miami providers needing focused compliance and protection.
Core Features
RD Cyber Consultants delivers HIPAA Risk Assessment and Compliance Services, Network Security with Fortinet Cisco Gigamon, Cloud Security with Azure, and CyberOps and SOC services for threat detection and incident response. They also provide security audits with vulnerability assessments and penetration testing to quantify risk and prioritize fixes.
Pros
- Healthcare specialization: RD Cyber Consultants specializes in healthcare cybersecurity, so their recommendations align with HIPAA rules and common clinical workflows used by Miami medical offices.
- Longstanding experience: With over 19 years of industry experience, they bring institutional knowledge that helps reduce audit findings and accelerate remediation timelines.
- Bilingual support: English and Spanish support lowers communication friction for diverse staff and improves training uptake across multilingual teams.
- Around the clock support: Their 24/7 support availability helps minimize downtime and speeds incident response for clinics that operate outside typical business hours.
- Documented outcomes: They show proven results in HIPAA compliance and security improvements, which helps justify budget approvals to practice owners and compliance officers.
Cons
- Limited pricing transparency: Public information is sparse beyond a starting price of $3,000 for HIPAA risk assessments, which makes budgeting for ongoing services difficult.
- Healthcare centric: Their strong focus on healthcare reduces applicability for accounting or legal firms that need industry agnostic controls or different regulatory frameworks.
- Support channel details: Customer support channels are described as email, phone, and WhatsApp without clear escalation paths or dedicated portal access for large practices.
Who It’s For
Healthcare providers in South Florida seeking specialized cybersecurity services to achieve and maintain HIPAA compliance will get the most value. Multi office medical practices, home health agencies, and PPEC centers that require bilingual support and hands on remediation should consider RD Cyber Consultants.
Unique Value Proposition
RD Cyber Consultants combines deep healthcare regulatory knowledge with operational security tools from Fortinet Cisco Gigamon and Azure. That combination lets Miami medical practices close compliance gaps and reduce exposure to ransomware while keeping workflows familiar for clinicians and administrative staff.
Real World Use Case
A multi location medical practice in Miami engaged RD Cyber Consultants for a comprehensive HIPAA risk assessment. The engagement resulted in full compliance, zero audit findings, and an improved security posture that shortened the incident response time for phishing events.
Pricing
Pricing starts at $3,000 for a HIPAA Risk Assessment, with additional service pricing not published publicly. Practices should request a scoped proposal to compare remediation, managed SOC, and cloud security costs over a 12 month period.
Website: https://rd-cyber-consultants.com
CyberTrust Partners
At a Glance
CyberTrust Partners delivers industry-focused cybersecurity services with a clear emphasis on proactive protection and compliance. Their approach fits organizations that need a tailored program rather than a one-size-fits-all product.
Bottom line: a strong option for Miami medical, legal, and accounting firms that need policy driven security and managed monitoring, though some transparency gaps remain.
Core Features
CyberTrust Partners combines strategic guidance with hands-on security operations to build and maintain a company security program. Their offering covers policy creation, monitoring, user protection, and incident response.
- Cybersecurity Foundation including tailor made policies and compliance strategies.
- Asset and Network Management with continuous monitoring and security scripting.
- User Protection covering email security, phishing training, and safer browsing.
- Data Loss Prevention spanning dark web monitoring and cloud endpoint controls.
- Ransomware Protection through proactive scanning, device protection, and awareness training.
- Proactive Monitoring and Response with endpoint protection, smart alerts, and managed detection and response.
Pros
-
Tailored Industry Approach: The service adapts policies and controls to specific industry needs which helps meet sector rules like HIPAA and client expectations.
-
Comprehensive Service Suite: Monitoring, protection, and response are included so you can centralize vendor management and reduce overhead.
-
Proactive Threat Detection: Emphasis on managed detection and smart alerts helps surface threats before they escalate into incidents.
-
Versatile Industry Support: Serving healthcare, legal, insurance, and engineering shows the team can handle diverse regulatory requirements.
-
Educational Resources: Blog content and awareness training help raise staff vigilance and reduce human error on email and endpoints.
Cons
-
Website pricing is not listed so you must contact the vendor for a personalized quote which slows procurement timelines.
-
The site does not list certifications or partnerships that validate technical expertise which may matter for vendor risk reviews.
-
There is limited public detail about the specific technologies and platforms used which complicates third party assessment and tool integration planning.
Who It’s For
CyberTrust Partners is aimed at SMBs and professional firms that need a guided security program rather than point tools. It fits Miami doctors, lawyers, and accountants who must protect client data while meeting compliance and audit requirements.
Unique Value Proposition
They combine strategic policy work with managed operations so you get both governance and day to day protection. That mix helps practices reduce internal hiring while advancing security maturity and compliance readiness.
Real World Use Case
A healthcare provider adopted CyberTrust Partners to deploy a cybersecurity foundation, add data loss prevention, and enable proactive monitoring. The engagement helped align controls with HIPAA and reduced exposure to patient data exfiltration.
Pricing
Pricing is not specified on the website and requires contacting CyberTrust Partners for a personalized quote based on scope and industry needs.
Website: https://cybertrustpartners.com
CYPFER
At a Glance
CYPFER delivers rapid incident response and recovery services with a global in-house team available around the clock. The vendor focuses on recovery-led ransomware remediation and integrates closely with client operations to restore business continuity and reduce downtime.
Core Features
CYPFER combines incident response, ransomware recovery, and digital forensics into a single offering that supports complex breach scenarios. Their services include cloud and web app investigations, email compromise response, dark web monitoring, and data capture from threat actor infrastructure.
Pros
- Global 24/7 support: CYPFER provides continuous coverage with in-house specialists who deploy quickly to client sites when needed.
- Comprehensive service scope: The company covers incident response, forensics, ransomware recovery, and cyber risk management under one engagement.
- Seamless team integration: CYPFER positions itself as an extension of client operations, which helps reduce handoffs and decision delays during a crisis.
- Transparent approach: The vendor emphasizes trust and open communication to guide stakeholders through technical and legal steps.
- Proven experience: With more than 25 years in the field and 2,500 customers, CYPFER brings institutional knowledge to high-pressure incidents.
Cons
- Specific pricing details are not published publicly so organizations need to contact CYPFER for a custom quote.
- The website highlights a broad service range but does not list predefined packages or tiers that fit fixed budgets or procurement cycles.
- The public materials do not break down typical response timelines or SLA thresholds in detail which may complicate procurement comparisons.
Who It’s For
CYPFER is best suited for mid-sized to large enterprises that require full-service incident response and forensic capabilities. The ideal client prefers rapid onsite deployment and wants a vendor that acts as an integrated security partner during active breaches.
Unique Value Proposition
CYPFER’s main advantage is a recovery-first methodology backed by in-house specialists who avoid outsourcing. That structure supports faster decision making, coherent forensic chains of custody, and consistent communication across technical, legal, and executive teams.
Real World Use Case
A multinational corporation suffers a complex ransomware attack. CYPFER assembles its team rapidly, contains the intrusion onsite, conducts a forensic root cause analysis, and leads data recovery. The engagement concludes with a cyber risk assessment and prioritized prevention plan.
Pricing
Pricing is available by direct consultation and is listed as “Contact CYPFER for custom quote” in their public materials. Prospective clients should request a scoped proposal to align services with incident risk and budget.
Website: https://cypfer.com
Ridge IT
At a Glance
Ridge IT delivers military-grade security and managed IT services with a cloud first, zero trust approach aimed at regulated organizations. The platform is positioned as Tampa’s leading MSSP and claims protection for over 2.5 million users, which signals scale and operational maturity.
Fast local presence. That matters.
Core Features
Ridge IT bundles endpoint protection, threat detection and response, and managed IT services into a unified offering. The company supports cloud infrastructure scaling and migration and provides CMMC and federal compliance assistance for regulated contractors.
The firm highlights rapid response teams in Tampa, DC, Atlanta, and Miami and promotes a zero trust architecture implementation for regional clients.
Pros
- Military grade cybersecurity protections: Ridge IT advertises hardened defenses designed to meet high assurance requirements for sensitive workloads.
- Comprehensive and integrated platform: The product combines endpoint, detection, response, and managed services so you do not juggle multiple vendors.
- Fast, responsive local teams: Having presence in Tampa and Miami shortens time to remediation and improves on site coordination for audits and incidents.
- Transparent pricing and communication: The company emphasizes clear communication, which helps legal and accounting teams when documenting vendor controls.
- Recognized MSSP and Inc 5000 honoree: Third party recognition supports credibility when you must justify vendor selection to stakeholders.
Cons
- Specific service details and pricing are not publicly detailed, which makes budget planning and procurement approval slower for finance teams.
- Limited information about customizable options or the client onboarding process is provided in the available content, which leaves questions about adaptation for niche workflows.
- No explicit mention of free trial or demo options, reducing the ability to validate effectiveness before commitment.
Who It’s For
Ridge IT fits organizations that need enterprise grade protections and compliance support, especially government contractors, healthcare providers, and financial firms operating in Tampa or Miami. It also suits accounting and legal practices that must demonstrate structured vendor security controls to their clients.
Unique Value Proposition
Ridge IT combines regional rapid response with an emphasis on zero trust architecture and federal compliance support. For firms seeking local accountability plus the operational scale implied by millions of protected users, Ridge IT offers a single vendor approach to security and managed IT.
Real World Use Case
A Tampa defense contractor used Ridge IT to meet CMMC requirements while migrating sensitive workloads to a cloud first architecture. Ridge IT supplied endpoint hardening, continuous detection and a managed response plan, which reduced audit remediation time and centralized evidence for assessors.
Pricing
Pricing is not specified in the available content. Procurement teams in accounting, legal, and medical sectors should request detailed proposals and a scope of services to compare total cost of ownership and onboarding timelines.
Website: https://ridgeit.com
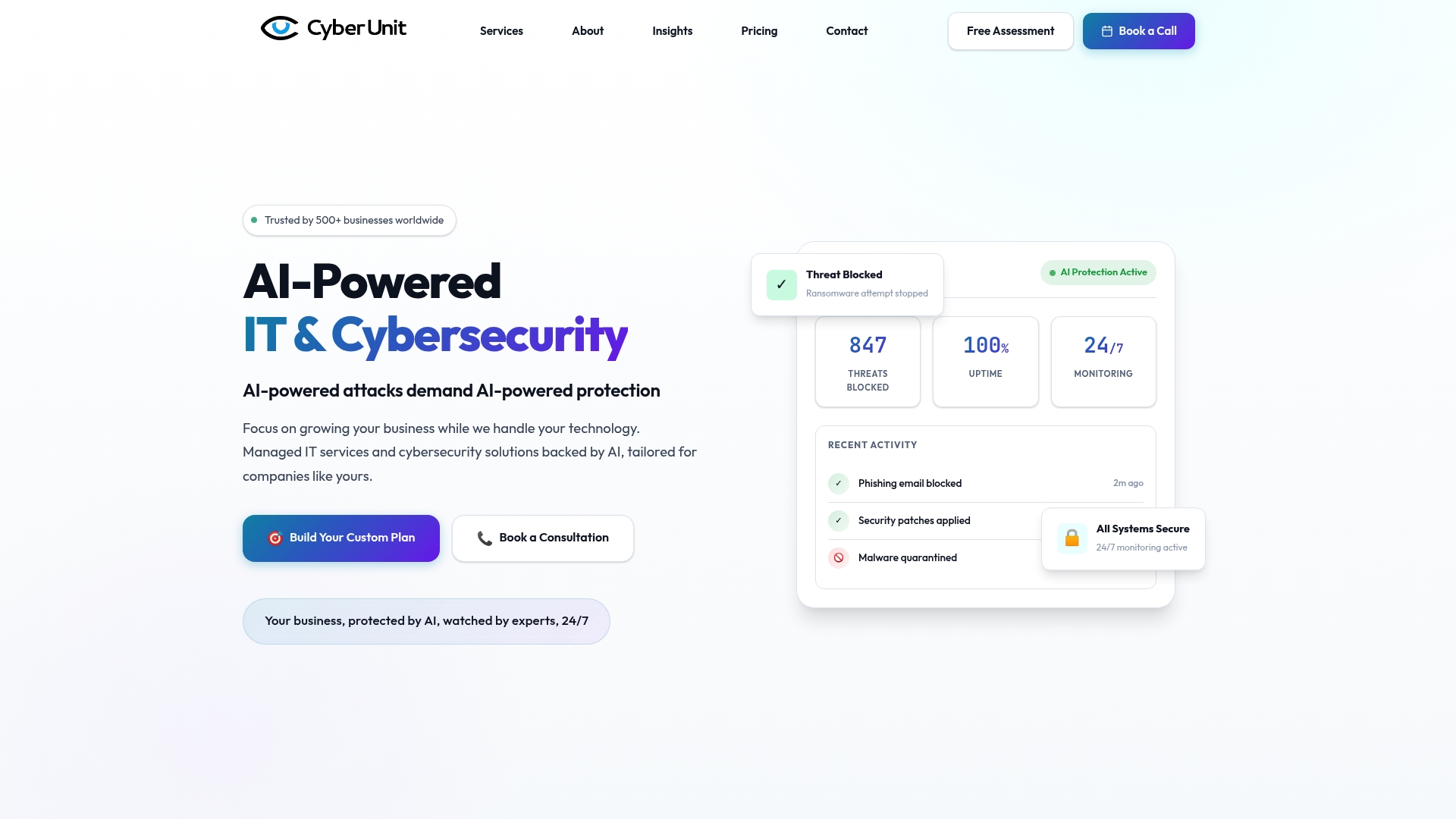
Cyber Unit
At a Glance
Cyber Unit delivers AI-powered attack protection and managed IT with 24/7 monitoring and expert support. The firm serves over 500 businesses worldwide and combines security assessments with ongoing threat detection to protect client infrastructure.
Cyber Unit fits organizations seeking a single vendor for proactive cybersecurity and managed IT support with local North America presence since 2008.
Core Features
Cyber Unit centers on AI-powered attack protection, managed IT services, and comprehensive cybersecurity assessments. Their stack includes vulnerability management and threat detection and response, described as EDR and MDR with continuous monitoring and expert incident response.
The company also offers customized plans and a proven methodology to align security controls with business needs.
Pros
- Trusted by 500+ businesses: The company’s client base shows broad adoption across industries and suggests repeatable delivery of services.
- Comprehensive service mix: Combining managed IT, vulnerability management, and threat detection reduces vendor overhead for IT teams.
- Proven methodology: Cyber Unit uses an established approach for cybersecurity and IT management that supports measurable improvements in resilience.
- Strong customer satisfaction: Over 106 five star reviews indicate reliable support and positive client experiences.
- Customized plans: Tailored service packages allow you to match coverage to specific compliance needs and risk profiles.
Cons
- No specific product details exist for individual tools or software, which makes technical comparisons difficult for procurement teams.
- Pricing varies based on custom plans and needs, so budget forecasting requires direct quoting from the vendor.
- Focuses primarily on B2B services, so the offering does not suit individual users or family protections.
Who It’s For
Cyber Unit targets small to medium sized businesses that need proactive protection and full IT management. IT managers in Miami accounting, legal, and medical firms will value the focus on tailored plans, compliance oriented assessments, and 24/7 monitoring to protect sensitive client records.
Teams with limited internal security staff will find the managed services and expert response useful for covering operations without hiring aggressively.
Unique Value Proposition
Cyber Unit packages security and IT under one roof, reducing complexity for busy IT leaders. The mix of AI detection, continuous monitoring, and consultative assessments creates a single point of accountability for prevention, detection, and remediation.
That unified model helps professional services firms protect client data while freeing internal teams to focus on business priorities.
Real World Use Case
A manufacturing company engaged Cyber Unit for a security assessment, remediation roadmap, and ongoing monitoring. Cyber Unit implemented vulnerability management, tuned EDR rules, and provided 24/7 response, which reduced incident volume and improved uptime for critical systems.
The engagement supported regulatory reporting and tightened controls around remote access for contractors.
Pricing
Pricing varies depending on the plan and services selected. Clients build custom packages with options for monthly, annual, and one time fees, so request a tailored quote to get accurate costs for your environment.
Website: https://cyberunit.com
Cybersecurity and IT Solutions Comparison
This table helps compare various cybersecurity and IT solutions to inform readers on offerings most suitable for professional service firms and organizations in Miami.
| Product Name | Core Features | Pros | Cons | Pricing |
|---|---|---|---|---|
| Transform 42 | Business operations automation, security controls | Automation saves 30% time; audit-ready compliance | Pricing not disclosed publicly | Custom-tailored per firm size and complexity |
| RD Cyber Consultants | Healthcare cybersecurity services, HIPAA compliance | Specialized in healthcare HIPAA rules; Bilingual support | Limited pricing transparency | Begins at $3,000 for HIPAA Risk Assessment |
| CyberTrust Partners | Policy creation, threat monitoring, incident response | Versatile industry support; tailored security programs | Website lacks tool-specific details | Requires contacting vendor for quote |
| CYPFER | Incident response, ransomware recovery, forensics | In-house 24/7 support; global experience | Pricing details not shared online | Quotes customized per client needs |
| Ridge IT | Military grade security, compliance assistance | Rapid local presence; Inc 5000 honoree | No customizable product package descriptions | Contact vendor for services pricing |
| Cyber Unit | AI-powered attack prevention, IT management | Trusted by 500+ businesses; Tailored service plans | B2B-focused, not suited for individuals | Pricing based on custom plans |
Unlock Scalable Cybersecurity with Strategic IT Partnership
The article “Top 6 Cyber Security Programme Manager Tools 2026” highlights key challenges like achieving audit-ready compliance, automation to save time, and scaling operations without increasing headcount. If you are a Doctor, Lawyer, or Accountant in Miami facing these hurdles, your growth depends on more than just point solutions. You need a partner who integrates security and automation directly into your workflows to deliver measurable results.
Transform 42 specializes in exactly this approach. We help you build capabilities that land larger clients and grow your monthly revenue by 7 to 8 figures while keeping your team lean. Learn how our all-in-one strategic IT service can give you a competitive edge at Transform 42. Take the next step now to reclaim your time and boost your firm’s cybersecurity sophistication.
Frequently Asked Questions
What are the key features to look for in cyber security programme manager tools?
Choose tools that offer automation capabilities, compliance tracking, and real-time monitoring to enhance your security posture. Ideal tools should help streamline operations and provide built-in controls for audit readiness.
How can I determine the best cyber security programme manager tool for my organization?
Evaluate your organization’s unique requirements such as team size, industry regulations, and specific security challenges. Create a checklist of necessary features and compare available tools to see which best meets your needs.
What benefits can I expect from using a cyber security programme manager tool?
Using these tools can help improve operational efficiency by automating tasks, reduce manual errors, and enhance compliance readiness. For example, effective tools can reclaim over 30% of time spent on routine security tasks.
How long does it typically take to implement a cyber security programme manager tool?
Implementation timelines vary by tool and organization complexity, but effective tools often promise rollout in weeks rather than months. Aim for a structured implementation plan to achieve operational improvements swiftly.
What type of organizations can benefit the most from cyber security programme manager tools?
Organizations that handle sensitive client data, such as legal firms, healthcare providers, and financial institutions, will find these tools particularly beneficial. They help meet compliance requirements while enhancing security measures to protect client information.
Are there specific compliance requirements these tools can help meet?
Yes, many cyber security programme manager tools are designed to assist with various compliance frameworks like HIPAA or GDPR. Evaluate tools for built-in compliance features that automatically align your operations with necessary regulations.