Three out of every four attacks now rely on valid credentials. For independent CPAs and financial consultants in Miami, this statistic reveals a harsh truth: your username and password combinations are the primary targets for cybercriminals. Traditional perimeter security no longer protects sensitive client data. This guide explains what zero trust means, why it matters for your practice, and how to implement its principles to enhance cybersecurity measures and compliance for your clients.
Table of Contents
- What Zero Trust Means: Core Principles For CPAs And Financial Consultants
- How Zero Trust Architecture Works: Models And Components Relevant To Financial Firms
- Why Zero Trust Matters For CPAs And Financial Consultants: Benefits And Challenges
- Implementing Zero Trust In Your CPA Or Financial Consultancy Firm: Practical Steps And Best Practices
- Enhance Your CPA Firm’s Cybersecurity With Expert Guidance
- Frequently Asked Questions About Zero Trust For CPAs
Key takeaways
| Point | Details |
|---|---|
| Zero trust never assumes trust by default | Every user, device, and access request must be continuously verified regardless of network location. |
| Identity attacks dominate financial services | Credential abuse is the leading breach vector, making traditional perimeter defenses insufficient. |
| Implementation follows a phased approach | Start with identity verification, device posture checks, and network segmentation before expanding. |
| Least privilege reduces attack surfaces | Granting minimal necessary access limits damage potential and accelerates compliance. |
| Challenges include complexity and costs | Legacy system integration, resource demands, and user resistance require careful planning. |
What zero trust means: core principles for CPAs and financial consultants
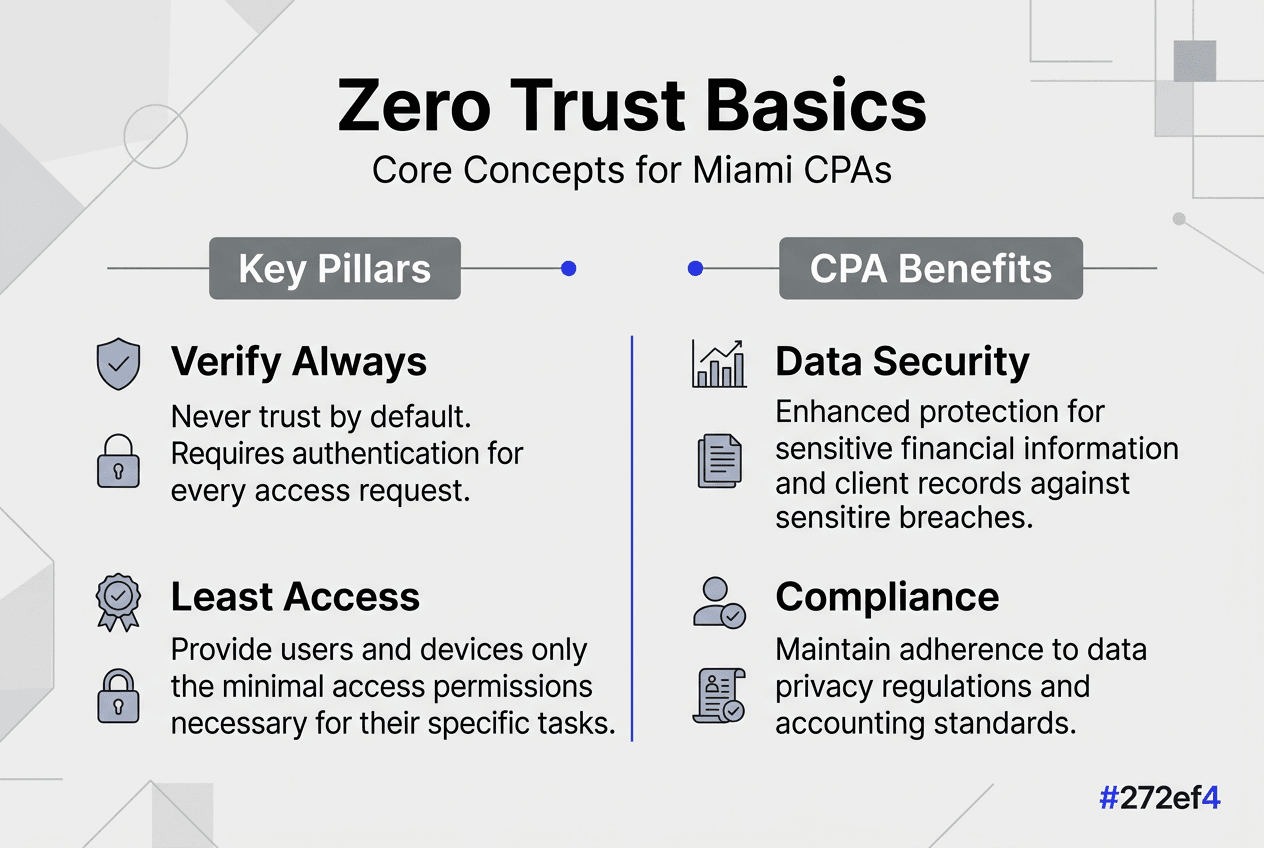
Zero trust is a security model that eliminates implicit trust. Unlike traditional security that trusts users inside the network perimeter, Zero Trust Architecture assumes no implicit trust regardless of location, credentials, or device. This fundamental shift matters for Miami financial professionals handling tax returns, financial statements, and confidential client data.
The core principle is simple yet powerful: never trust, constantly verify. No user or system receives automatic trust, whether they work from your office or remotely. Every access attempt triggers verification checks before granting entry.
Key zero trust concepts include:
- Continuous verification of identity and device posture at every access point
- Least privilege access, granting only the minimum permissions needed for specific tasks
- Micro-segmentation, dividing networks into isolated zones to contain breaches
- Explicit verification instead of assumed trust based on network location
Traditional perimeter security fails for financial professionals because threats often originate from compromised credentials of legitimate users. Once attackers breach the perimeter, they move laterally across your network, accessing sensitive client files and financial records. Zero trust stops this lateral movement by requiring verification at every step.
“Zero trust transforms security from a castle-and-moat approach to a verify-every-time model, crucial for protecting the sensitive financial data CPAs handle daily.”
For Miami-based practices, this approach directly addresses compliance requirements under regulations like the Gramm-Leach-Bliley Act and IRS cybersecurity guidelines. By verifying identity and device health before every data access, you create audit trails that demonstrate due diligence. Learn more about implementing zero trust security specifically for accountants.
How zero trust architecture works: models and components relevant to financial firms
Understanding how zero trust operates helps you evaluate solutions for your CPA firm. NIST SP 800-207 defines core ZTA components: Supporting Infrastructure, Policy Enforcement Point (PEP), Policy Administrator (PA), and Policy Engine (PE). These work together to make access decisions.
The Supporting Infrastructure includes identity management systems, security information databases, and threat intelligence feeds. The PEP acts as a gatekeeper, allowing or blocking access based on PA decisions. The PA evaluates policies and instructs the PEP, while the PE analyzes trust signals and access context to determine whether requests should be approved.
NIST provides three major deployment models for implementing zero trust:
| Model | Description | Best for |
|---|---|---|
| Software-Defined Perimeter (SDP) | Creates individualized network perimeters per user/device | Firms with remote staff needing secure client portal access |
| Microsegmentation Architecture | Divides networks into small isolated zones with granular policies | Practices with on-premises servers requiring containment |
| Enhanced Identity Governance (EIG) | Focuses on robust identity verification and conditional access | Smaller firms prioritizing identity protection over infrastructure |
These models differ in complexity and enforcement granularity. SDP works well for practices with distributed teams accessing cloud-based tax software. Microsegmentation suits firms with legacy accounting systems requiring network-level isolation. EIG offers the quickest wins for small practices by strengthening identity controls without major infrastructure changes.
Pro Tip: Start your zero trust journey by focusing on identity governance and basic segmentation. These deliver measurable security improvements without requiring complete infrastructure overhauls, making them ideal first steps for independent CPA practices.
For Miami financial consultants, choosing the right model depends on your technology stack and risk profile. Cloud-based practices benefit from SDP, while hybrid environments may need microsegmentation. Understanding how security architecture redefines digital transformation helps align your zero trust approach with business growth.
Why zero trust matters for CPAs and financial consultants: benefits and challenges
Credential abuse remains the most common breach vector targeting financial professionals in 2026. When attackers steal or guess passwords, they walk through your digital front door looking like legitimate users. Zero trust stops this by requiring continuous verification, even after initial login.
Key benefits of zero trust for your practice:
- Strict access control limits who can view sensitive client data
- Least privilege principles reduce the blast radius if credentials are compromised
- Enhanced threat detection through continuous monitoring of user behavior
- Faster containment when suspicious activity is detected
- Improved compliance posture with detailed access logs and verification trails
The principle of least privilege and efficient threat detection make zero trust particularly valuable for CPA firms handling confidential tax information. By granting minimal necessary access, you minimize what attackers can steal even if they breach one account. Continuous monitoring flags unusual behavior, like a staff account suddenly accessing hundreds of client files at midnight.
“Zero trust transforms reactive security into proactive protection, verifying every access attempt to prevent credential-based breaches before they cause damage.”
However, implementing zero trust involves real challenges. Complex implementation, high costs, and employee pushback are common obstacles for smaller practices. Many CPAs operate with lean IT budgets and limited technical staff, making comprehensive zero trust deployments seem overwhelming.
Challenges financial firms face adopting zero trust:
- Integration complexity with legacy accounting and tax software systems
- Initial costs for identity management platforms and security tools
- Resource requirements for ongoing policy management and monitoring
- User friction from additional verification steps during busy tax season
- Knowledge gaps in cybersecurity architecture among non-technical staff
Despite these challenges, the benefits outweigh the costs for practices serious about protecting client data. Starting small with identity governance and expanding gradually makes zero trust accessible even for independent practitioners. Florida CPAs can explore zero trust security tailored to their specific regulatory environment to understand local compliance advantages.
Implementing zero trust in your CPA or financial consultancy firm: practical steps and best practices
Successful zero trust adoption requires a phased approach rather than wholesale replacement of existing security. Zero Trust implementation often begins with identity, device posture, and segmentation, allowing you to build momentum with early wins before tackling complex integrations.
Phased implementation roadmap:
-
Identify and classify sensitive assets: Map where client data lives, who accesses it, and what access levels they need. Include tax returns, financial statements, bank records, and personal identifying information.
-
Strengthen identity verification: Implement multi-factor authentication for all staff accounts. Deploy single sign-on solutions that centralize identity management. Consider adaptive authentication that adjusts verification based on risk signals.
-
Assess and enforce device posture: Verify that devices accessing your systems meet security baselines. Check for updated operating systems, active antivirus, and disk encryption before allowing network access.
-
Segment your network: Separate client data storage from general business systems. Create isolated zones for different sensitivity levels. This contains breaches and simplifies compliance auditing.
-
Apply least privilege access: Review and reduce permissions so staff can only access data required for their specific responsibilities. Remove standing administrative access and implement just-in-time elevation for special tasks.
-
Deploy continuous monitoring: Implement logging and alerting for unusual access patterns. Monitor for after-hours access, geographic anomalies, or bulk data downloads that signal compromise.
-
Establish governance and policy enforcement: Document access policies clearly. Train staff on new verification procedures. Create incident response plans specific to zero trust alerts.
Zero Trust works as a phased strategy because you can start with quick wins like MFA and gradually expand to advanced capabilities. This approach spreads costs over time and allows your team to adapt without overwhelming disruption during critical periods like tax season.
Pro Tip: Engage your staff early in the zero trust planning process. Explain how stronger security protects both client data and their personal information. Address concerns about workflow friction upfront and gather feedback on verification steps to reduce pushback during rollout.
One size does not fit all. Zero Trust must be tailored to your firm’s specific risks and compliance needs. A solo practitioner working with individual tax clients faces different threats than a mid-sized firm serving corporate clients with complex financial structures. Scale your zero trust implementation to match your risk profile, budget, and technical capabilities.
Miami CPA firms can explore specialized cybersecurity practices for protecting client data and review comprehensive zero trust security guides for accountants to develop customized implementation plans.
Enhance your CPA firm’s cybersecurity with expert guidance
Implementing zero trust security in your Miami practice doesn’t require you to become a cybersecurity expert overnight. Professional IT consulting helps you adopt zero trust principles efficiently while maintaining compliance with financial industry regulations.
Specialized consultants bring expertise in risk assessments, technology integration, and compliance management tailored to CPA firms. They identify your highest-risk access points, recommend appropriate zero trust tools that integrate with your existing accounting software, and create policies that protect client data without disrupting workflows during busy seasons.
Benefits of partnering with strategic IT consultants:
- Faster implementation through proven frameworks and best practices
- Cost efficiency by avoiding trial-and-error with incompatible tools
- Ongoing support for monitoring, policy refinement, and threat response
- Compliance expertise ensuring your zero trust approach meets regulatory requirements
Explore business transformation services designed specifically for Miami CPAs to see how technology partnerships can enhance your security posture while supporting practice growth. Professional guidance reduces the complexity of zero trust adoption for accountants, letting you focus on serving clients while experts handle the technical details.
Frequently asked questions about zero trust for CPAs
What is zero trust security in simple terms for financial professionals?
Zero trust is a security approach that requires verification for every person and device trying to access your systems, regardless of whether they’re inside or outside your network. Instead of trusting users once they log in, it continuously checks identity and device health before allowing access to client data.
How does zero trust improve client data security and regulatory compliance?
Zero trust reduces breach risk by limiting access to only what each user needs and continuously monitoring for suspicious behavior. This creates detailed audit trails showing who accessed what data and when, which satisfies compliance requirements under regulations like Gramm-Leach-Bliley and demonstrates due diligence to regulators and clients.
What does zero trust implementation cost and how long does it take?
Implementation timelines range from three to twelve months depending on practice size and existing infrastructure. Small practices can start with identity improvements for $2,000 to $5,000 initially, while comprehensive deployments for larger firms may require $20,000 to $50,000 plus ongoing management costs. Phased approaches spread expenses and allow gradual adoption.
How does zero trust differ from traditional firewall and antivirus security?
Traditional security trusts users once they pass the perimeter (like a firewall), similar to a castle moat protecting everything inside. Zero trust treats every access request as potentially hostile, verifying continuously even after initial login. This stops attackers who steal credentials from moving freely through your network.
Where should small CPA firms start with zero trust?
Begin with multi-factor authentication for all accounts and basic network segmentation separating client data from general systems. These foundational steps deliver immediate security improvements without massive infrastructure changes. Then gradually add device posture checks and more granular access controls as resources allow.
Recommended
- Zero Trust Security: 56% Fewer Insider Breaches For FL CPAs
- Zero Trust Security: Complete Guide For Accountants – Stratgetic IT Consultants For Accountants
- Complete Guide To Cyber Security For Miami CPAs – Stratgetic IT Consultants For Accountants
- Understanding SOC 2 AICPA: Your Guide to Compliance
- SOC 1 Report Example: Boosting Trust in Tech Compliance